Brand Impersonation and Clone Website: What It Is, How It Affects Your Revenue, and How to Stop It
06.03.2026
Contents
Imagine a potential customer searching for your product or service in Google. They type in your brand name, click on a result or a branded ad, and end up on a page with your logo, your color scheme, and an HTTPS certificate that makes it appear legitimate. All as intended, right?
**Except that’s not your actual page. It’s a clone website. **
That is the simple explanation of what brand impersonation looks like. An attack on your branded traffic that can severely damage your company’s reputation, ROI, and revenue.
So how likely is your brand to become a target, and how do you prevent that from happening? In this article, we will explore just that. We’ll dive into how impersonation attacks operate, which brands are most vulnerable to them, and what monitoring tools are required for an effective brand protection strategy.
What Is Brand Impersonation?
When an unauthorized actor deliberately mimics a legitimate brand to deceive users, divert traffic, and capture revenue, it’s called brand impersonation. It leverages the brand’s credibility, using logos, color schemes, website layouts, and domain names to create a seemingly authentic experience and deceive users.
The objectives vary:
-
• Traffic capture — redirecting users to monetized pages
-
• Data extraction and phishing — collecting credentials or payment details
-
• Revenue diversion — stealing transactions
-
• Affiliate attribution hijacking — deploying unauthorized tactics to claim last-click credit
Impersonation attacks are particularly effective because they intercept high-intent traffic. A user searching for a specific brand already demonstrates purchase intent. Diverting that traffic means intercepting the most valuable segment of the funnel.
The effectiveness of brand impersonation hinges on visual familiarity. A website clone looks indistinguishable from the original at first glance. If branding, layout, and checkout flow feel consistent, the page is perceived as legitimate. And if a clone website is supported by fake PPC ads targeting trademark keywords, the perception of legitimacy increases.
Brand Spoofing vs. Brand Impersonation
These terms are often used interchangeably, but they describe different levels of imitation.
Brand spoofing typically involves partial identity misuse. An attacker may replicate a brand’s name in ad copy, mimic email sender details, or register a lookalike domain that resembles the original. The goal is to appear connected to the brand without necessarily recreating the full experience.
Brand impersonation, by contrast, is more complex. It often includes:
-
• A clone website that mirrors layout, structure, and navigation
-
• A typosquatting domain name
-
• Paid ads that reuse official messaging or trademarked terms
Brand spoofing may appear as unauthorized brand bidding or misleading ad copy. Full impersonation typically involves website cloning supported by ads or SEO positioning to capture high-intent traffic.
For brands, the impact differs. Spoofing can inflate CPC and dilute impression share. A full clone website can redirect conversions, capture user data, and destroy customer trust.
Types of Brand Impersonation You Should Know
Below are the common formats observed in real-world cases. Each format targets a different stage of the acquisition funnel — from search visibility to final attribution.
Website Cloning
Through a website cloner setup, attackers recreate product pages, checkout flows, and trust signals. A clone website is hosted on a lookalike or unrelated domain and promoted via paid ads, SEO, or redirects. Because it appears to be the same website users are familiar with, they often complete the funnel before realizing anything is wrong.
What it can look like: A user clicks a branded search ad and lands on a site visually identical to the original ecommerce store. Payment is processed through an external gateway, and the brand never sees the transaction — but absorbs the reputation damage when the product never arrives.
Typosquatting
Typosquatting relies on registering domains that differ by one character or slight spelling variations. These domains may host thin content, redirect to competitors, or serve as infrastructure for impersonation attacks. In paid search, typosquatted domains often support unauthorized brand bidding campaigns.
What it can look like: A user types the brand name with a minor spelling error. Instead of reaching the official site, they land on a parked page monetized with competitor ads or are redirected through an affiliate tracking link that captures commission.
Misleading PPC Ads
Unauthorized advertisers bid on trademarked keywords and use brand terms in ad copy to simulate affiliation. The landing page may be a reseller, a lead arbitrage funnel, or a clone website. Even when the final page is not fraudulent, the campaign interferes with cost efficiency and attribution clarity.
What it can look like: A third party runs search ads targeting “[Brand] official site” queries. The ad copy implies partnership, but traffic is redirected through an intermediary page that inserts affiliate tracking before sending users to the legitimate site.
Social Media Impersonation
Fraudsters create social media profiles using brand logos, product images, and similar handles. These accounts run sponsored posts or respond to user inquiries, directing traffic to external pages. Social impersonation often works in parallel with search campaigns to reinforce perceived legitimacy.
What it can look like: A user clicks a paid Instagram ad from what appears to be the brand’s account. The landing page mimics the official store and promotes limited-time discounts, collecting payment details without delivering goods.
Affiliate-Based Brand Impersonation
Here, impersonation attacks exploit affiliate infrastructure. The objective is to intercept attribution. Tactics include:
-
• Ad cloaking and brand bidding activity
-
• Using redirect chains to overwrite attribution
-
• Deploying landing pages that resemble the official site
What it can look like: An affiliate bids on trademark keywords in violation of program terms. Traffic passes through a redirect that drops tracking cookies before sending users to the official site, capturing commission for demand the brand generated itself.
Marketplace Impersonation
On ecommerce marketplaces, impersonators list products under the brand name using copied visuals and descriptions. In some cases, they distribute counterfeit goods. In others, they hijack existing listings. Marketplace impersonation often complements search campaigns that drive traffic directly to those listings.
What it can look like: A sponsored search result leads users to a marketplace listing branded as the official store. The seller is unauthorized, pricing is inconsistent, and product quality damages customer perception.
Email Brand Spoofing
Email-based brand spoofing involves forging sender addresses, logos, and formatting to mimic official communications. It may promote fake offers or request credential updates. While traditionally categorized as phishing, it frequently integrates with paid traffic and domain impersonation setups.
What it can look like: During a major sales period, customers receive emails about “exclusive discounts.” Links lead to a website clone designed to capture login credentials, later used for account takeover or payment fraud.
Brand Impersonation in Search Results and PPC
Search is the primary distribution layer for impersonation.
High-intent queries, predictable user behavior, and auction-based visibility create a controllable acquisition channel — not only for brands, but also for attackers. When impersonation infrastructure intersects with search, the impact shifts from reputational risk to measurable revenue loss.
In Organic Search
Organic search remains a powerful vector because it inherits user trust. Many users still associate top-ranking results with legitimacy.
A clone website indexed by search engines can rank for branded queries, especially when supported by aggressive backlink generation or technical SEO optimization. In some cases, attackers replicate metadata, structured data, and even FAQ schema to increase CTR.
Queries such as “Brand login,” “Brand discount code,” or “Brand official site” are frequently targeted. Fraudulent website clones optimized around these modifiers can rank quickly, especially in less competitive regions.
From a brand protection strategy perspective, organic impersonation is difficult to detect without systematic SERP monitoring across geographies and devices. Manual checks rarely capture dynamic ranking shifts.
In PPC Campaigns
Unlike organic SEO, which requires indexing and ranking cycles, PPC provides immediate visibility. With sufficient budget, impersonators can position themselves above the official brand ad within hours.
Brand campaigns typically deliver the highest CTR and lowest CPA in an account. Industry benchmarks show that branded queries achieve significantly higher click-through rates than non-branded terms — often multiple times higher. This makes them attractive targets for brand spoofing.
Unauthorized advertisers may:
-
• Bid on trademarked keywords
-
• Use brand terms in ad copy
-
• Imitate official messaging
-
• Lead to a clone website or intermediary funnel
Because paid ads often appear above organic results, users encounter fraudulent pages before the legitimate domain. As a result, PPC becomes a distribution multiplier for impersonation attacks.
Without continuous monitoring — including brand bidding protection and ad hijacking detection — impersonation remains embedded inside normal auction dynamics.
Which Brands Are at Risk?
Brand impersonation concentrates where intent, trust, and transaction volume intersect. Brands that dominate search, invest heavily in PPC, operate affiliate programs, and generate high LTV create valuable ecosystems that fraudsters seek to exploit.
Certain industries show structural vulnerability because users regularly search for login pages, booking confirmations, invoices, or shipping updates — queries that can be easily replicated through impersonation attacks.
Data from Guardio shows which industries and brands were targeted the most in 2025. Below we list them and explain the reasoning behind their high attractiveness for fraudsters:
1. Technology & Social Media
Microsoft, Google, Meta (Facebook), Apple, Amazon, and Adobe were heavily targeted in phishing campaigns. Attackers frequently used fake security alerts and invoice notifications. These brands benefit from massive branded query volumes and habitual login behavior. That combination lowers user skepticism and increases susceptibility to brand impersonation phishing.
2. Gaming & Digital Services
Roblox and Steam were heavily targeted, particularly for account takeover and in-game reward scams. Gaming platforms are attractive because of younger user bases, stored payment methods, and strong emotional attachment to accounts.
3. Retail & Logistics
Amazon and DHL saw consistent impersonation activity, especially during peak shopping periods. Shipping confirmation scams remain one of the most scalable formats of email and PPC-based brand spoofing. Retailers experience sharp traffic spikes during holidays, which attackers mirror with fraudulent landing pages and paid ads.
4. Luxury Goods
Coach was identified as the most impersonated luxury brand during the holiday season, followed by Dior and Ralph Lauren. Luxury brands combine high average order value with aspirational demand. A single successful website clone can generate significant transaction value before detection.
5. Financial & Payment Services
Coinbase, PayPal, and E-ZPass experienced high impersonation rates related to financial theft. Financial brands attract impersonation not only because of transaction volume, but because users are conditioned to quickly respond to account alerts.

The Business Impact of Brand Impersonation
The impact extends across multiple budget lines:
- Revenue loss and conversion leakage: As impersonation attacks often target users already searching for a specific company, they intercept demand that marketing teams have already paid to generate. FairWinds estimates that typosquatting alone accounts for $327 million in annual losses — that includes lost impressions and revenue, as well as ineffective marketing decisions based on distorted data.
- Rising PPC costs: When impersonators bid on trademarked keywords, auction pressure increases. Even if the official ad maintains top position, additional bidders raise minimum CPC thresholds. Over time, this shifts branded campaigns from low-cost defensive channels to contested auctions.
- Customer data exposure: Brand impersonation phishing introduces a separate category of risk: credential and payment theft. For subscription-based businesses, stolen credentials can result in account takeover scenarios that inflate churn and reduce lifetime value.
- Reputational impact: Users rarely differentiate between an official site and a fraudulent one when trust is breached. If a customer interacts with what appears to be the same website they used before and experiences fraud, brand perception declines. In competitive markets, trust erosion directly affects acquisition efficiency.
- Legal and compliance consequences: Enforcement carries its own cost structure. Domain disputes, clone website takedown procedures, and litigation generate direct legal fees. FairWinds research estimates UDRP-related spending as $79 million a year.
How to Prevent Brand Impersonation
According to TAG, industry-wide anti-fraud programs helped save $10.8 billion in ad fraud losses in a single year. This demonstrates that prevention works — and that its impact can be measured.
The basic components for preventing brand spoofing and impersonation attacks are strategy and technology.
Brand Protection Strategy
A brand protection strategy is a cross-functional operating model connecting marketing, compliance, and performance teams.
At minimum, it should include:
-
Continuous monitoring that covers branded keywords in SERP and PPC, newly registered typosquatting domains, affiliate traffic sources, and redirect paths.
-
Regular audits performed monthly or quarterly to assess branded traffic in SERP and PPC.
-
Clear affiliate rules that define restrictions on trademark bidding, prohibited ad copy language, rules regarding redirects and cloaking, and consequences for non-compliance.
-
Structured documentation containing evidence for escalation: screenshots of fake PPC ads and clone websites, records of typosquatting domains, redirect chains, timestamps.
Brand Monitoring Tools
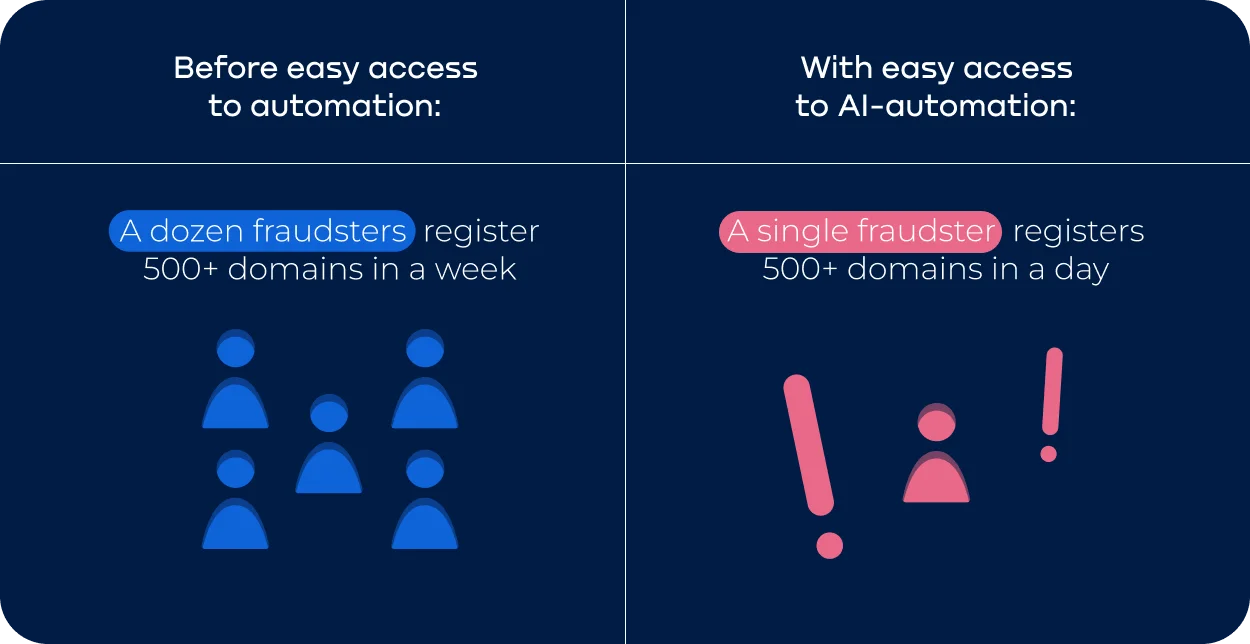
Manual checks cannot keep pace with automated impersonation infrastructure: a website cloner can produce new copies in just a couple of clicks. In 2025 Netcraft identified more than 4,300 malicious domains launched by a single actor, with 511 made in just one day.
Brand monitoring tools provide scalable oversight across channels and can alert teams as soon as suspicious activity starts.
Your monitoring workflow should include:
-
• Domain monitoring
-
• SERP monitoring
-
• Affiliate compliance tracking
Tools that combine these layers into unified reporting reduce fragmentation across teams. Platforms such as Bluepear integrate SERP monitoring, brand bidding protection, ad hijacking detection, and affiliate oversight into a single analytical framework.
How Bluepear Helps Prevent Brand Impersonation
Preventing impersonation attacks requires visibility across search auctions, organic results, and affiliate flows — combined with evidence strong enough to support enforcement. Bluepear is built around that operational requirement. It is a self-service platform that fits easily into day-to-day workflows, provides clear reporting straight to email or Slack, and makes detection of impersonators simple and fast.
Rather than focusing on isolated incidents, the platform monitors the full acquisition layer where impersonation typically emerges:
- • Brand bidding protection: Bluepear continuously tracks branded keyword auctions across locations and devices. It identifies third parties bidding on restricted brand terms and ad copy using trademarked words.
- • Ad hijacking detection: Bluepear captures redirect chains, cloaking, and brand spoofing.
- • Affiliate monitoring: Bluepear tracks affiliate traffic, identifying abnormal patterns in click-to-conversion paths.
- • SERP visibility control: SERP monitoring provides fake websites detection through tracking of branded queries across search engines that can reveal suspicious domains that use brand keywords in snippets or on-page.
Bluepear provides screenshots, time-stamps, redirect path records, and affiliate tracking data. This evidence accelerates takedown requests, affiliate enforcement actions, and platform complaints.
For brands operating at scale, early detection directly protects budget efficiency and attribution integrity. Give Bluepear a try to identify vulnerabilities in your brand protection before they translate into financial loss.

Conclusion
Brand impersonation is evolving at a pace that manual oversight can no longer match. AI-generated clone websites and scalable phishing kits are now capable of creating hundreds of near-identical pages in hours.
The future of brand protection depends on systematic, automated monitoring. Integrating real-time detection, cross-channel visibility, and evidence-based enforcement transforms response from reactive to proactive.
FAQ
Is brand spoofing the same as brand impersonation?
Brand spoofing is focused on visually or contextually mimicking a brand to deceive users, often in a single channel like email or social media.
Brand impersonation is broader, encompassing any unauthorized use of a brand across websites, PPC ads, affiliate networks, and other digital channels to divert traffic, steal data, or exploit customer trust. While all spoofing instances qualify as impersonation, not all impersonation relies solely on spoofing.
What are the telling signs of a clone website?
A website clone replicates the look and feel of an original site but often has subtle differences: unusual domain extensions, inconsistent URLs, typos, outdated content, or missing security headers.
Users may be drawn in by identical logos, SSL certificates, and familiar design, but inconsistencies in page behavior, broken links, or prompts for unnecessary credentials can reveal the fraud.
What is a website cloner and is it illegal?
A website cloner is a tool or script that copies the content, layout, and sometimes functionality of an existing website to create an unauthorized replica.
While some cloners are used legitimately for backups or testing, using them to mislead users, intercept transactions, or divert traffic constitutes brand impersonation and is illegal under intellectual property and anti-fraud laws. Enforcement often involves takedown requests, UDRP claims, and evidence collection for potential civil or criminal proceedings.

